Edith Cowan University
School of Science
crypto system代写 Crypto currencies include two important parts namely: block chaining and block mining. you will be using Python.

Task
For this task you will be required to simulate a crypto currency system using Python.
Crypto currencies include two important parts namely: block chaining and block mining. A cryptocurrency network is a decentralised system and there is no central authority to verify transactions. Individuals are free to add new transactions which get broadcasted to the entire network. All transactions must be signed and subsequently verified for legitimacy. Only legitimate transactions are included in new blocks and illegal transactions are rejected.crypto system代写
Block miners continuously listen for new legitimate transactions transmitted through the communication network between the participating miners, and combine previous hash values and transaction details to compute a unique nonce value that solves the complex computation problem set by the cryptocurrency miner algorithm.crypto system代写
The first miner who successfully computes (mines) the correct nonce, broadcasts the new block (previous hash + transactions + proof of nonce calculation work), leading to an update of all transaction entries for all users of the cryptocurrency network. The first successful miner gets rewarded (in cryptocurrency) for the computational effort put in for calculating the correct nonce.crypto system代写
Including the hash of the previous block in new blocks is referred to as block chaining.
This ensures transactions are not tampered with, as any changes to transactions will change the hash of dependent blocks. The block mining process includes listening for new transactions and combining the hash of previous blocks and the transaction data, and then finding the nonce that solves the problem of providing the proof of work. Bitcoin mining or block mining serves to add new blocks as well as release new bitcoins.crypto system代写
Furthermore, in a decentralised bitcoin network, adding new blocks to the global block chain requires the consensus of more than half the mining power. Refer to this YouTube video by 3Blue1Brown to get a better idea of block chaining and crypto currencies. The image below shows a sample block-chaining process.crypto system代写
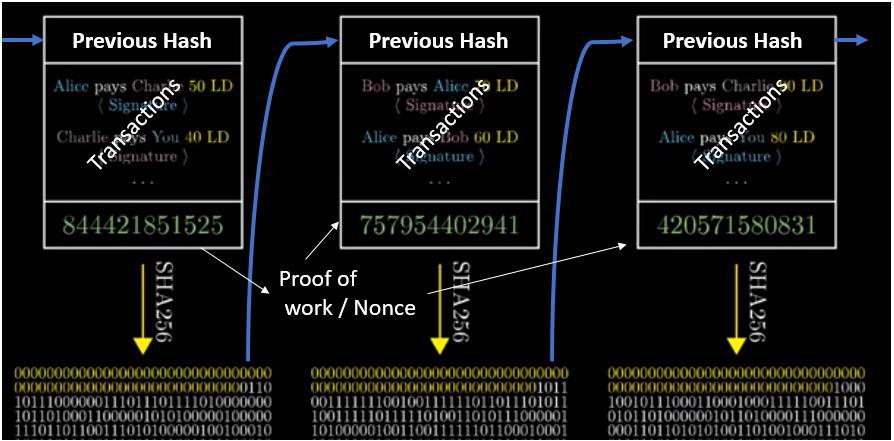
Figure: Blockchaining process illustrated.
This workshop requires you to develop a Python-based cryptocurrency system that has two components:
- Transaction recording program
- Block mining program
Transaction recording program
The main role of this program will be to collect information from the users for new transactions (prompting users to enter the below details through the command prompt) and storing this information into a transaction file. The transaction data should have the following information:
- From (username of person sending the cryptocurrency amount)
- To (username of person receiving the cryptocurrency amount)
- Amount
- Timestamp
This program should do the following:
- Loop continuously to prompt the user if a new transaction needs to be added to the chain.
- If yesprompt for: FROM name, TO name and AMOUNT to send.
- Store the transaction details to a transaction file in the current directory.
- Provide option to quit the program during its flow.
Block mining program
This program constantly checks the transaction file for new transactions. Once new transactions are detected, the mining program combines the hash of the previous block and the transaction data and then calculates the correct nonce for the block. The successful SHA-256 hash will be added to the next block.crypto system代写
The blockchain file (BC) should include the successful blocks. Each block should contain the following information:
- Block Index
- Data
- Previous block’s hash (using SHA256)
- Nonce (calculated using a mining function)
When the mining program is first executed, it will need to create the first block with an index 0 and an arbitrary previous hash value. (See instructions below.) The program should comprise the following steps:
- Create a BlockChain (BC) file in the current directory
- Check the BC file to see if any previous blocks already exist. If not, create the first block with an index = 0, data = “first block”, current time stamp and the SHA-256 hash of “first block”. Add the hash of the first block to the BC file. Add this block to the BC file and store the hash value somewhere you can access it for the next block.
- When new transaction data is detected, calculate the nonce that produces a SHA-256 (previous block’s hash + transaction data + nonce) hash which contains 14 zeros (inhex). (Why 14 zeroes? Because it is an arbitrary number that we have chosen for CSI 2108, and it adds to the computational work that needs to be done to find the hash value of the above tuple: previous block’s hash + transaction data + nonce). Refer to the nonce calculation pseudocode given below.
- Add the successful hashblock to the blockchain file. This should include all the information described above that belongs in a block. Store the successful hash value of the block somewhere you can access it for the next block.
- Continuously loop though these steps to add blocks comprising new data unless the user wants to exit.
Pseudocode of nonce calculation function: Create a new block = (index + timestamp + transaction data + previous block’s hash) Initialise a nonce variable to zero Continuous loop: Update block by concatenating the nonce Calculate the SHA-256 of the updated block Check if the message digest (i.e. the hex value of the hash) has 14 zeros: Update the BC file with the successful block Store the hash value (you will need this for the next block) Break Check if the nonce value exceeds 50000 (this step is performed to prevent an infinite loop): Update the BC file with last produced hash Break Increment the nonce
Requirements
You must include the following with your submission:
- The source code for your implementation of the block chaining a mining system.
- Documentation explaining your implementation. This should explain each of the stepsin your program, what it does, and any implementation choices you made. Note that you are also welcome to comment your code, but this will not excuse you from writing the documentation!
- Instructions for running your program to complete the required objectives.
| Marking key: | ||
| • | File handling | (2) |
| • Using appropriate hashing libraries from Python | (2) | |
| • | Block formation | (3) |
| • | Nonce calculation | (4) |
| • | User interaction | (2) |
| • | Correct results | (2) |
Submission
Your assignment must be submitted via the appropriate link on Blackboard.crypto system代写

Referencing
Your work must comply with ECU referencing guidelines and plagiarism policy. If you use sources outside of this worksheet to help you with your answers, make sure you include references to these sources at the bottom of your assignment. (You should also include in-line citations to indicate which source you have used for which section.) Failure to do so will be considered a breach of academic integrity.crypto system代写
更多其他: 数据分析代写 Report代写 Review代写 Case study代写 Proposal代写 Academic代写



您必须登录才能发表评论。